Protection and peace-of-mind for your business.
Forth Tech’s approach to cyber security is to follow the NIST Cyber Security Framework (CSF) standard. The five NIST functions of identify, protect, detect, respond, and recover all work concurrently and continuously to form the foundation for successful cybersecurity risk management.
NIST Cyber Security Framework (CSF)

Request a FREE consultation on any IT matter
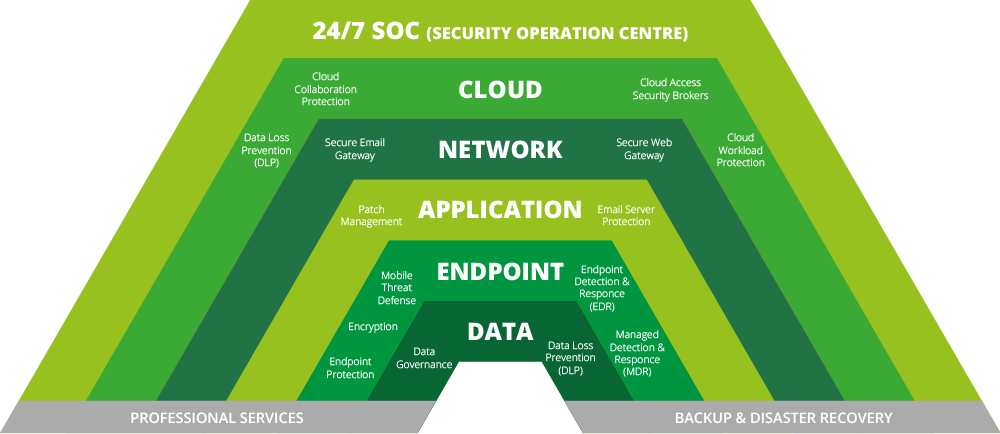
Our Multi-Layered Security Approach
IT environments consist of multiple layers – Data, Application, Endpoint, Network and Cloud etc. Unless each layer is secured, it’s a cyber-attack waiting to happen, spelling damage to brand, reputation and revenues.
Our cyber security support package adds an additional layer to our standard IT support package giving you an extra level of business security:
Why choose Forth Tech for Multi-Layered Security?
Best of Breed Solutions Across All Layers
We enable you to assemble best of breed solutions that protect every layer. Here’s why you should choose Forth Tech: